Rachit Arora
Projects
These are the projects which I have done/Working on. Those are listed down below
Talks & Ctfs
All the talks I presented and CTFs I created for various conferences like OWASP, Defcon, RSA.
You can find the repository here: github.com/rach1tarora/ctfs-talks.
Offensive Coding
I maintain a GitHub repository called “Offensive Coding” where I have various coding projects I’ve worked on. These projects include tools for Windows and Linux, shellcoding, Python scripting, and much more.
You can find the repository here: github.com/rach1tarora/offensive-coding.
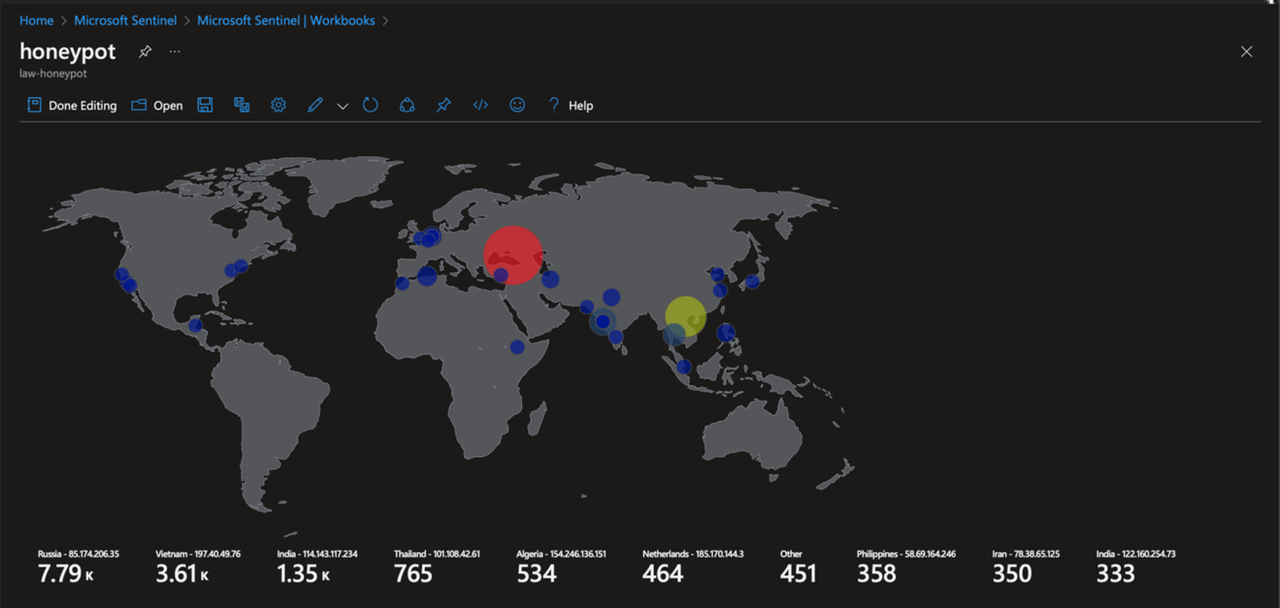
Sentinel Heatmap (RDP Bruteforce)
During my college, I created a project on Azure that monitors and records all attempted RDP (Remote Desktop Protocol) bruteforce attacks, and then presents this data as a heatmap for easy visualization.
More information and the report: here.
Tempus CTF
Created a CTF for NSS, which involved Forensic Analysis, Cryptography, and Privilege Escalation (Docker Container Breakout).
More information about the challenge and the badge: here.
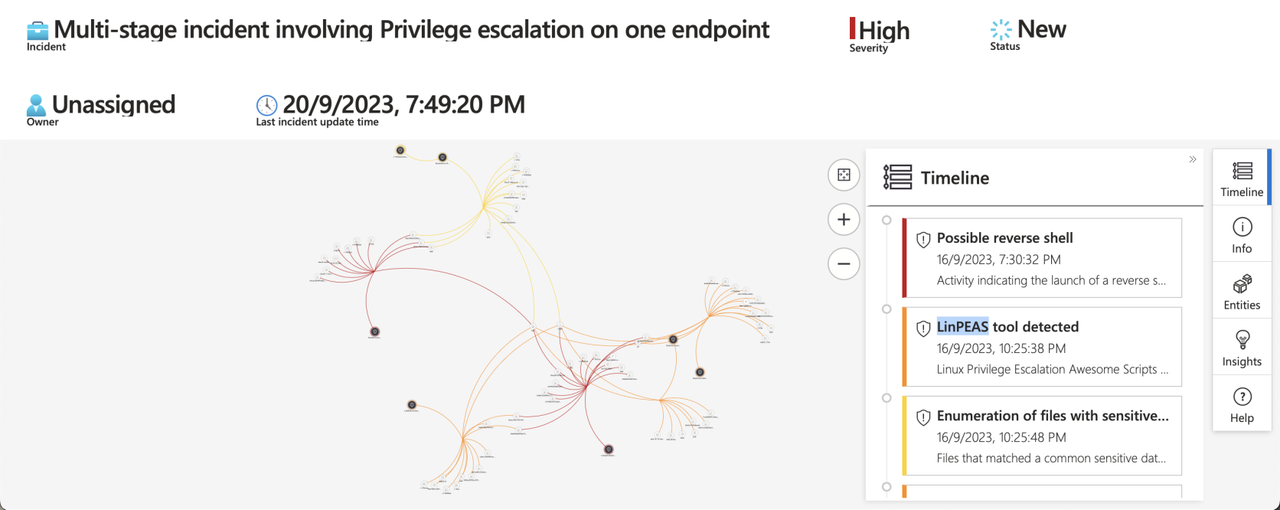
A blog has been published: here, analyzing the observations drawn from individuals attempting to compromise the VM.
Active Directory Homelab
Gained hands-on experience and established a strong foundation by setting up an Active Directory Homelab.
Learnt about Enumeration, Lateral Movement, Domain Privesc, and Persistence.
Practiced attacks like Kerberoasting, AS-REP Roasting, and DCSync and utilized tools like BloodHound, SharpHound, Powerview, and ADModule.
Fixed the vulnerabilities to explore the defensive aspect of the process.